The Challenge of Securing Transactional Data
Transactional data, including credit card details, is often targeted by cybercriminals. Breaches can lead to significant financial loss, reputational damage, and non-compliance penalties. The challenges include:
- Unsecured Access Points: External users, including contractors and partners, often access systems remotely, increasing vulnerability.
- Data Transmission Risks: Data in transit between end users and backend systems can be intercepted.
- Compliance Requirements: Regulations demand strict controls to ensure the confidentiality and integrity of client data.
The CVAD Approach: A Secure Site with DMZ, NetScaler, and Jump Box
1. DMZ Design for Isolation
A Demilitarized Zone (DMZ) serves as the first line of defense, isolating external traffic from the internal network.
- Purpose: The DMZ hosts public-facing services, such as the Citrix Gateway (NetScaler), to ensure that unauthorized users cannot directly access sensitive systems.
- Implementation: Deploy Citrix Gateway in the DMZ to handle authentication and secure connections before allowing access to internal resources.
2. Citrix ADC (NetScaler) for Secure Access
- SSL VPN: Encrypts data traffic between the user and the CVAD environment.
- Multi-Factor Authentication (MFA): Adds an extra layer of security to ensure that only authorized users access the system.
- Granular Access Control: Policies can be defined to allow access based on user roles, locations, or device posture.
3. Jump Box for Controlled Access
- Purpose: It ensures that users never directly access sensitive data or applications but work within an isolated session.
- Configuration:
- Deploy a hardened jump box in the DMZ.
- Users log in to the jump box to access CVAD-hosted applications or desktops.
- Screen captures, clipboard functions, and file transfers can be restricted to minimize data leakage risks.
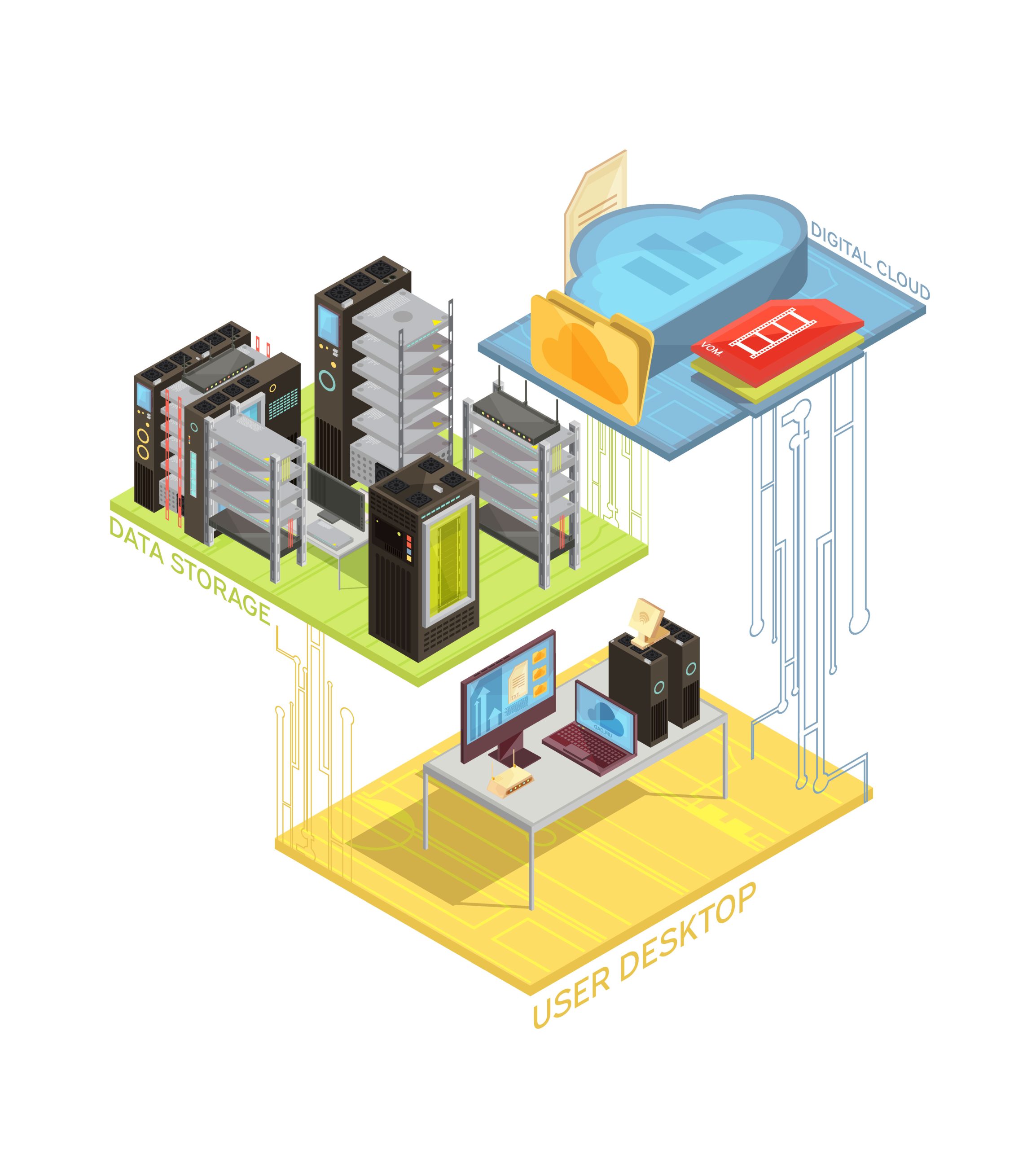
4. CVAD Deployment for Centralized Management
With CVAD, sensitive applications handling transactional data remain centralized within the data center, never stored on local endpoints.
- Secure Applications: Applications that process transactional data are virtualized and isolated from end-user devices.
- Policy Enforcement: CVAD allows IT to enforce policies that restrict printing, USB usage, or screen sharing.
- Monitoring: Citrix Director provides real-time insights into user activity, ensuring anomalies are detected promptly.
Benefits of This Approach
- Enhanced Data Security:
- The centralized deployment ensures that sensitive data never leaves the controlled data center environment.
- NetScaler encrypts traffic and adds advanced security layers with MFA and contextual access policies.
- Compliance with Regulations:
- The architecture meets PCI DSS and other compliance requirements by implementing access controls, encryption, and activity monitoring.
- Simplified User Access:
End users, including external contractors, can securely access transactional systems through a streamlined process using the jump box. - Scalability and Flexibility:
The architecture supports scaling up to meet increased demand without compromising security.
Conclusion
Securing transactional data in today’s digital landscape requires a proactive and layered approach. By leveraging Citrix Virtual Apps and Desktops with DMZ design, NetScaler, and a jump box for controlled access, enterprises can build a secure, compliant, and efficient environment. This architecture not only protects sensitive client information but also ensures seamless access for end users, enabling organizations to meet their business and security objectives effectively.